Category Archives: Bottled at source
The best things in life come from source.
Russia is Trying to Destroy Kyiv – Committing a Monstrous Crime
Cold weather, warm hearts
As one might remember, last week Trump said that he asked Russian President Vladimir Putin to not strike Ukraine for a week, and Putin agreed to that. Days later, of course, Russia unleashed yet another mass aerial attack. When asked about that, Trump nevertheless said Putin “kept his word.” Kyiv groaned a collective “WTF?” at this. One Ukrainian politician aptly called it a “mockery of our misery.”
https://www.biznews.com/global-citizen/ronnie-aptekerukraines-war-feye-witness
This week saw the continuation of trilateral peace negotiations in Abu Dhabi, where representatives of Ukraine, Russia and the U.S. came together to discuss ending the war. This is the second round of this specific attempt at negotiations — hosted by the United Arab Emirates, and taking place after a reshuffle in the Ukrainian delegation. What we witness is a performance, meant for one spectator: U.S. President Donald Trump. The Ukrainian delegation is forced to go on with it to show Trump that Ukraine is not an obstacle to peace. Russia, on its part, uses the “negotiations” to buy time and not give the U.S. an incentive to introduce more sanctions or increase its backing of Ukraine.
Home Alone
I am back in Kyiv. It is very very cold, and everyone is on edge.
Electricity, heating and water are on and off, and who knows how much more the infrastructure can handle. If the evil Russians successfully strike more of the heating plants and electricity stations, then God knows how people are going to make it until the end of winter.
I am happy to be in Kyiv in our home here, but I feel alone. Perhaps it is the cold weather. Perhaps it is the mood. Perhaps it is the world. No one seems to care. I am sure people do care, but Ukraine certainly doesn’t get enough support. If they did, people would not be suffering like this. Children and the elderly are having a very difficult time. The country is exhausted. People are worried. The word “apocalypse” often comes up in conversation.
I was reading an update from an inspired writer I follow from the Kyiv Independent – I am cutting and pasting her words here :
“The resilience narrative is a trap. Not the idea itself – the actual daily practice of continuing under impossible conditions. That’s real, and it’s necessary, and we’re doing it because there’s no alternative. What’s dangerous is the way that word gets deployed by people watching from safety to make sense of our suffering. It’s a heroic term, an honorable one even.
But like all words that get used too much, it starts to obscure more than it reveals.
When you read about Ukrainian resilience, I need you to know: none of us here are doing okay. We are functioning, which is not the same thing. We go to work because rent is still due. We go to parties because the alternative is staring at walls, waiting for the next air raid siren. We maintain relationships, pursue careers, argue about restaurant choices, complain about traffic – all the ordinary friction of life continues because if we stopped to fully metabolize what’s happening, we would dissolve. We would become puddles of grief on the floor, unable to move, and that’s not a metaphor. That’s a real possibility we each avoid through sheer force of will and the accident of having obligations that won’t wait.
On top of every wartime worry – where is the person I love, will the power stay on, will that sound be thunder or something worse – people still carry all the peacetime worries too. The difficult neighbors, the failing relationships, the aging parents, the children who won’t sleep, the bills they can’t pay. The war doesn’t pause these problems, it just makes them harder to solve and less appropriate to mention in certain social circles.
So we continue. Not because we’re resilient, but because stopping means drowning, and we’ve decided – collectively, stubbornly, perhaps foolishly – that we’d rather stay afloat until the day we can finally breathe again.
That day comes when the Kremlin burns. Not metaphorically. Not diplomatically. Actually burns.
Until then, we tread water and call it living.”
It is totally surreal being here now. I will share more thoughts soon.



Nobody wants peace more than Ukrainians
Kyiv is being hit every other night. Russian missiles and drones are trying to destroy the infrastructure and also residential buildings are being attacked. People are dying. And many are suffering. Children and the elderly in particular. It is a very cold winter in Ukraine and so many buildings are without heating, electricity and water.
The Russian invasion of Ukraine is soon going to be in its fifth year, and the world has stopped caring. Well, at least, the world’s politicians. I mean, there are these farcical peace talks taking place as I write this, and somehow no one raises an eyebrow and condemns Russia for the constant evil attacks on Ukraine. We don’t see anyone putting pressure on Russia to stop. What we do see is Trump putting pressure on Ukraine, claiming that “Zelensky doesn’t want peace”. Peace could come right now if Russia simply stops attacking Ukraine. Ukraine poses no threat to Russia.
These current nonsense peace talks are nothing more than an attempt by Ukraine and its European allies to prevent the Trump administration from accusing Kyiv of being unwilling to achieve peace, walking away from the process, and even cutting off assistance to Ukraine. The truth is, all these so-called negotiations are with America, not Russia. The Russians are just there to try and waste time. They also keep up their bullshit story that they want peace. How come if Russia wants peace they keep bombarding Ukraine, and how come Trump and his gang turn a blind eye to it. WTF ?!
What a shameful state of affairs.
“It’s not ok to watch an entire nation being bombed into freezing in brutal subzero temperatures.
It’s not ok to pretend russia wants peace while it targets homes, hospitals, and energy grid, aiming to destroy the Ukrainian nation.
It’s not ok to delay air defences while civilians sleep in cold shelters and darkness.
It’s not ok to care more about bloody russian money than the lives of Ukrainian children.
It’s not ok to reward an aggressor with lands and people.
It’s not ok to normalize war crimes, mass graves, and deported children.
So many things happening around are utterly wrong, pushing the prospects of real peace further away.“
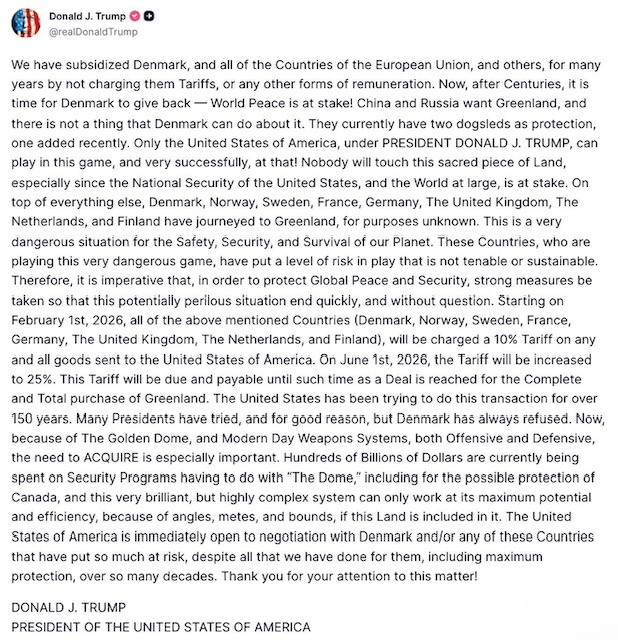
Dump Trump
Trump is insane. And yet so many Americans will follow him off a cliff. He could decide to attack a random country because they were “mean to hm”, like Norway. His madness knows no limits and he is just warming up. The world still has 3 more years of this lunatic.
The thing is, if America collapses, we are all in shit. Just think of all the investment funds that are tied to America and the US Dollar.
If Trump does want to invade another country then will the US military refuse such an order. Could American soldiers be ordered to kill Europeans?
Trump got angry because he was not awarded a Nobel Prize. Can you imagine what else could trigger this maniac. Someone looks at him funny and the next thing there is an attack.
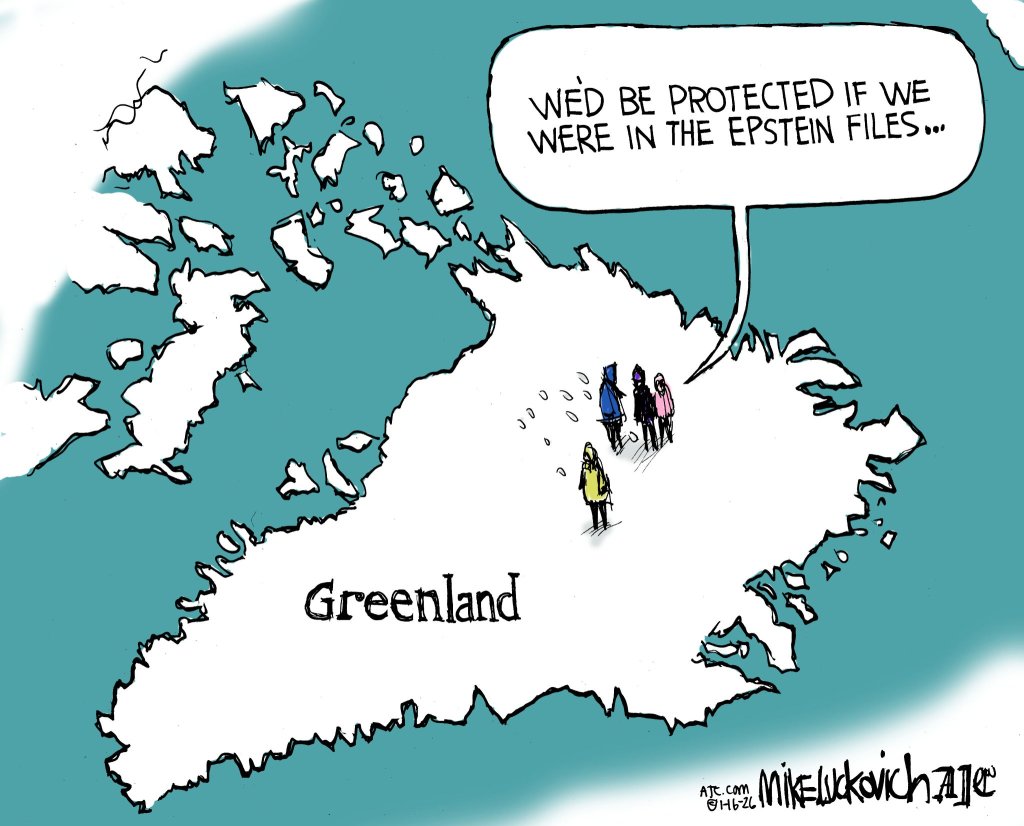
Think of Greenland like Ukraine’s Crimea. If Trump does take over Greenland then it will not stop there.
Are we all over-reacting when it comes to Trump? It sure looks though like he is doing what he is telling the world he wants to do. Just like Putin. And Hitler. Nobody believed these people but perhaps we should. Trump has unlimited power and he can do whatever he wants. I reckon this is exactly what he will do … whatever he wants. The warning signs are all there.
“Historically it’s a fact you have stop dictators right at the start otherwise it leads to war! Europeans should have stepped in immediately when Russia started using proxies to take land in Ukraine, then then Russia got away with shooting down a civilian airline plane and then annexing Crimea and of course Russia invades Ukraine full on and then the Europeans wake up but America still thinks appeasement is the right option to resist Russian aggression. Putin has been using Hitler’s playbook since 2016! Did nobody bother to look at events in the 1930’s that lead to WW2.
This is a strange world for someone like me who grew up in a world where lines were drawn and no one was allowed to cross them. Korean war, Suez Canal war, Vietnam, Cuba missile crisis, etc. Not a perfect world but there was some order. Then the West decided we are all the same so let’s win over our adversaries by commercial ties and make friends with Russia and China. These two embraced the opportunity to enrich themselves without becoming democratic but the main problem is both have the same crazy world domination plan deep within their psyche. China got back Hong Kong and look what happened and now they still want Taiwan and be the next colonial power.
Russia now just wants to go back to the USSR and take over all the Eastern Bloc countries.
That old story tale this all up: A scorpion meets a turtle at the edge of a river and asks for a ride across a river but the turtle says, no because you can sting me and I would drown! The scorpion says but I would die too as I can’t swim! The turtle says yes, that makes sense so come aboard and I will get you across . When they were half way across the river the scorpion stung the turtle and as they were both dying the turtle asked why did you do that you have killed us both and the scorpion said it’s my nature!“
He is going to try cancel the mid-terms … just watch
Trump is going to keep on pushing the envelope because no one stops him. The tech bros and big oil are working him and greed is the name of the game. It is all going to coming crashing down. You can’t cheat nature forever.

“Yes, NATO is dead now.
And the final nail in its coffin was driven by the biggest useful idiot the Kremlin and Beijing have ever had in the history of the Western world.
He did it out of his megalomania, ultra-vulgarity, his hunger for the easiest money and the cheapest attention, shallowness, ignorance, and an addiction to self-glorification in front of TV cameras, which has long since crossed into madness.
He did it out of sheer amorality, too: an insatiable urge to humiliate, humiliate, humiliate those who depend on him, for nothing but petty self-affirmation — while groveling before powerful and criminal enemies, just to get a scrap of their approval and feel like he belongs among the big bad guys.
But his is not the end. It is the beginning of a new alliance in a new world, a change that has been overdue for far too long.
The nations that remain faithful to the values of the free world will stay together.
And now, on the front line of that defense, stands Ukraine, with unmatched experience of the warfare of a new era, and a military exceptional in its resilience and heroism against one of the largest and most relentless war machines in human history.“
Enter the Dragon
Party Party Party
Imagine there was a public company. Let’s call it FunnyMoney Inc.
FunnyMoney didn’t do anything – it was just a share that people bought and sold. In short, a pubic company that only existed for the public to buy and sell its shares.
Yup, FunnyMoney did ZERO. It was just a share that people trade. And here is the first kicker: the hype is so intense that the market cap of all the shares in Funny Money Inc is around two trillion dollars.
People use this share to get drugs on the dark web, and pay assassins, and buy weapons, etc. This is all done anonymously and no government regulates the trade of FunnyMoney shares.
Yup, it is a free-for-all that has got a value of 2 trillion USD.
Yes, this is all hypothetical. How could this ever be a real thing … ?!
Another thing: it could all come tumbling down at any point but no one seems to care.
People send money from one country to another where there are exchange regulations, by trading FunnyMoney shares. It appears to have no rule of law. Just some kind of online just tech magic that bamboozles everyone, including the elderly, who want to buy FunnyMoney shares, because, well, the buzz is that it is a great investment. “It is all good” is what everyone says, including the US President. It must be a solid thing indeed!
And the craziest thing is that a tiny group of people hold 90% of the FunnyMoney shares and no one knows who these people are. Are they good, wholesome people? Who knows, and again, no one seems to care. As long as the money madness continues it is one big party. It is all just money money money.
There is one thing to keep in mind. For some technical reason (the subject of a future blog) the electricity required for the trade (transactions) of the FunnyMoney shares is very hectic, but again, who cares.
Now, think about Bitcoin for a moment. There is not much difference between this crypto front-runner and this hypothetical FunnyMoney story.
The truth about Bitcoin is that most transactions are about buying drugs and weapons and other illegal things. Circumventing exchange controls is another use case for Bitcoin. And for 99% of people it is a purely speculative investment fueled by nothing but hype. And Crypto gets even crazier and more hype fueled the further you get away from plain Bitcoin.
This new year ahead is going to be wild.
Stuff the fundamentals. It is time to party.
So keep on dancing, but make sure you are dancing very close to the door.

Not even one week in … this year is gonna make last year look like a walk in the park
Trump is just warming up. That is my view. And unless he is stopped, he will not stop. The same as Putin.
Here are some postings I read online :
Wanna hear a joke?
International law.
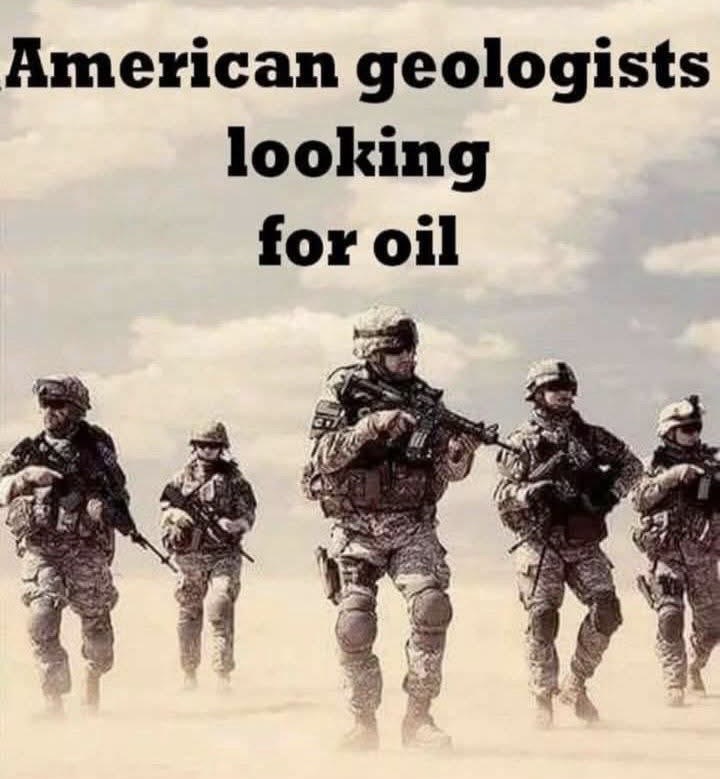
Let’s be clear: the Trump Admin is lying to the American people. This has never been about stopping drugs from coming to the US — it’s about grabbing Venezuela’s oil for his billionaire buddies. Trump has put American troops in harm’s way to boost oil company profits. Outrageous.
It’s not about drugs. If it was, Trump wouldn’t have pardoned one of the largest narco traffickers in the world last month. It’s about oil and regime change. And they need a trial now to pretend that it isn’t. Especially to distract from Epstein + skyrocketing healthcare costs.
Trump removed Maduro from power but is refusing to recognize Venezuela’s democratically elected president as the new president. Trump only wants to swap out an anti-American dictator with a pro-Trump dictator in Venezuela so he can take their oil. If you ever wondered what the United States would be like without a functioning Congress or Supreme Court, now you know.
Saddam wasn’t removed for ‘freedom’ – he started selling oil in Euros. Gaddafi wasn’t bombed for ‘human rights’ – he threatened the dollar with a gold-backed African currency. Maduro wasn’t targeted because of ‘democracy’- Venezuela dared to sell oil in Yuan and step outside U.S. financial control. Every time someone messes with the petrodollar, they magically become a dictator overnight. Call it what it is, racketeering with flags. ‘Liberation’ is what they sell to the evening news.
You know America has a huge problem when a quarter of the country went from worshiping GOD to worshiping a mentally unstable pedophile with the intellect of a rotten garden salad.
Mark Kelly is spot on. Like Trump, Nicolás Maduro is a despotic scumbag. By kidnapping Maduro, Trump just made the world infinitely more dangerous. The stupidity of Trump’s attack, kidnapping, occupation, and plundering and pillaging of Venezuela’s oil and natural resources cannot be understated. With Putin and Xi now seeing what they can get away with, the world is horrified.
I’m guessing we’re about to learn Greenland’s prime minister is also a narco-terrorist.
Whoever leaks the unredacted Epstein files in full might just end up saving the entire world.
Hear me out: Maybe it’s the United States that needs a regime change? Believing Trump bombed Venezuela to stop drug trafficking is like believing he redacted the Epstein files to protect the victims.
I have a 5 year old son. I wonder about the world he is going to grow up in. God knows how to guide him. I would like to teach him that honesty is the most important thing. Honest and integrity. But if I look at what is going in the modern world I don’t see much of that. What I do see is greed and bullshit.